Migrate Fortinet Firewall with the Firewall Migration Tool in Security Cloud Control
The Firewall migration tool in Security Cloud Control allows migrating configurations from Fortinet firewall to threat defense devices managed by your cloud-delivered Firewall Management Center. You can manually derive the configuration file from your Fortinet firewall and upload it to the migration tool to begin with your migration. To learn about supported Fortinet firewall configurations, see Fortinet Configuration Support.
Select Source Configuration
On the Select Source Configuration page, choose Fortinet (5.0+) and click Start Migration. Click Upload to choose the Fortinet configuration file and click Next.
Select Target
In the Select Target page, the cloud-delivered Firewall Management Center provisioned on your Security Cloud Control tenant is selected by default, and the Firewall Threat Defense devices managed by that management center are listed. You can choose the Firewall Threat Defense device you wish to migrate the configuration to, and proceed with the migration.
Note that the threat defense devices listed are displayed either as In Use or Available based on whether the device is being used in another migration instance. However, you can perform an override by clicking Change Device Status, selecting the device from the In Use list, and clicking Continue, which will make the device available for being selected as the target. Choosing Proceed without FTD pushes only NAT objects, ACLs, and port objects to the cloud-delivered Firewall Management Center. For more information about the commonly used ASA features and their equivalent threat defense features, see Cisco Secure Firewall ASA to Threat Defense Feature Mapping guide.
Caution | Changing the device status from In Use to Available impacts the ongoing migration instance that is using the device already. We recommend that you exercise caution when doing this. |
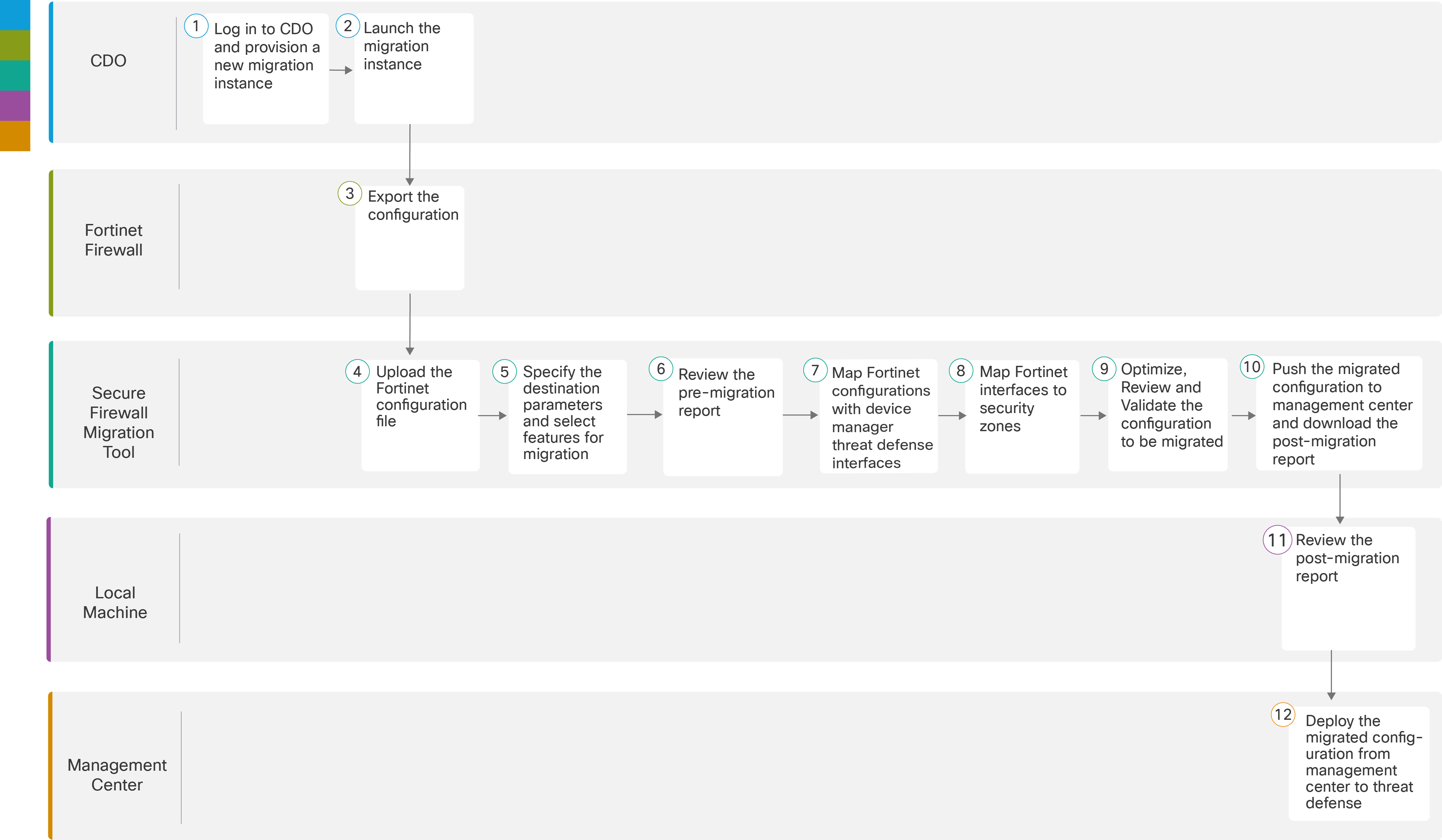
The flowchart that follows illustrates the step-by-step procedure for migration Fortinet firewall configurations to threat defense devices:
To perform the procedure with more detailed steps, continue to Export Fortinet Firewall Configuration from Fortinet Firewall GUI in Migrating Fortinet Firewall to Secure Firewall Threat Defense with the Migration Tool guide.
|
Workspace |
Steps |
|
|---|---|---|
| Security Cloud Control |
Log in to your Security Cloud Control tenant, and in the left pane, click , and click the blue plus |
|
|
Security Cloud Control |
After your migration instance is ready, click Launch and choose Fortinet (5.0+). |
|
|
|
Fortinet Firewall |
Export the Fortinet configuration to the local system. To export the configuration from Fortinet firewall, see Export the Configuration from Fortinet Firewall. |
|
|
Secure Firewall Migration Tool |
Upload the Fortinet config file exported from Fortinet firewall, see Upload the Fortinet Configuration File. |
|
|
Secure Firewall Migration Tool |
In this step, you can specify the destination parameters for the migration. For detailed steps, see Specify Destination Parameters for the Secure Firewall Migration Tool. . |
|
|
Secure Firewall Migration Tool |
Navigate to where you downloaded the pre migration report and review the report. For detailed steps, see Review the Pre-Migration Report. |
|
Secure Firewall Migration Tool |
To ensure that the Fortinet configuration is migrated correctly, map the Fortinet interfaces to the appropriate threat defense interface objects, security zones, and interface groups. For detailed steps, see Map Fortinet Firewall Configurations with Secure Firewall Device Manager Threat Defense Interfaces. |
|
|
|
Secure Firewall Migration Tool |
Map the Fortinet interfaces to the appropriate security zones, see Map Fortinet Interfaces to Security Zones for detailed steps. |
|
|
Secure Firewall Migration Tool |
Optimize and review the configuration carefully and validate that it is correct and matches how you want to configure the threat defense device. For detailed steps, see Optimize, Review and Validate the Configuration to be migrated. |
|
|
Secure Firewall Migration Tool |
This step in the migration process sends the migrated configuration to the cloud-delivered Firewall Management Center and allows you to download the post-migration report. For detailed steps, see Push the Migrated Configuration to Management Center. |
|
|
Local Machine |
Navigate to where you downloaded the post migration report and review the report. For detailed steps, see Review the Post-Migration Report and Complete the Migration. |
|
|
Management Center |
Deploy the migrated configuration from the cloud-delivered Firewall Management Center to threat defense. |
 button to start provisioning a new migration instance.
button to start provisioning a new migration instance.